Shodan is a search engine that allows users to identify and query data on Internet-connected devices. It is often used by security researchers and IT professionals to discover and analyze Internet-connected devices, including industrial control systems and other specialized equipment. Although the data that tools such as Shodan collect is publicly available, bad actors and hackers can use this information to identify vulnerabilities and attack points on publicly exposed devices. With the increased use of connected devices in building management, these potential access points pose a risk to operational technologies in commercial real estate buildings.
If your building has Internet-connected heating, ventilation, and air conditioning (HVAC) systems or a Building Management System (BMS), you need to take steps to secure building networks and devices and protect your tenants from bad actors. For example, if a BMS is not properly secured, an attacker can gain access to it and manipulate temperature set points in the building, affecting working conditions and productivity. Although this type of attack might at first seem trivial, it can result in serious consequences in certain scenarios, such as for data center operations or the storage of perishable inventory.
Attackers often exploit one “weakest link” system with the goal of accessing a different connected system. For example, if an account owner uses the same credentials to log in to both the BMS and a company database, attackers could obtain login information from a compromised BMS device and then use it to access confidential company data. A notorious example is the 2013 Target attack where hackers were able to infiltrate the company’s network using credentials obtained from a compromised HVAC system. The data breach exposed approximately $40 million credit and debit card accounts and cost the company an $18.5 million settlement and $202 million in overall recovery costs.
These types of attacks can result in damage and production issues that add up to significant losses. However, in addition to the direct financial costs of these attacks, there are also reputational implications for the building owner or operator. If an attack is made public, it can damage company status and lead to loss of trust from customers, tenants, or other stakeholders.
The best remediation for these scenarios is a zero-trust architecture in which all systems are locked down and inaccessible to the Internet and require validation at every access point. By taking proactive measures to identify vulnerabilities and secure operational technologies, building owners and operators can reduce the risk of costly and reputation-damaging attacks.
Using Shodan for security insights
It is important to regularly use tools like Shodan to help identify any building devices that are publicly exposed. You can sign up for a free Shodan account and run simple queries on their global index. Here are some ideas as a starting point for your search:
- Company name
- Building names
- Manufacturer of your BMS
- Names of smart building applications that run on-premises
- Vendors that provide hardware and sensors
For example, on the Shodan dashboard we searched for a common BMS provider. The resulting reports show device data including geographic location, network ports, organization names, specific product models, and much more.
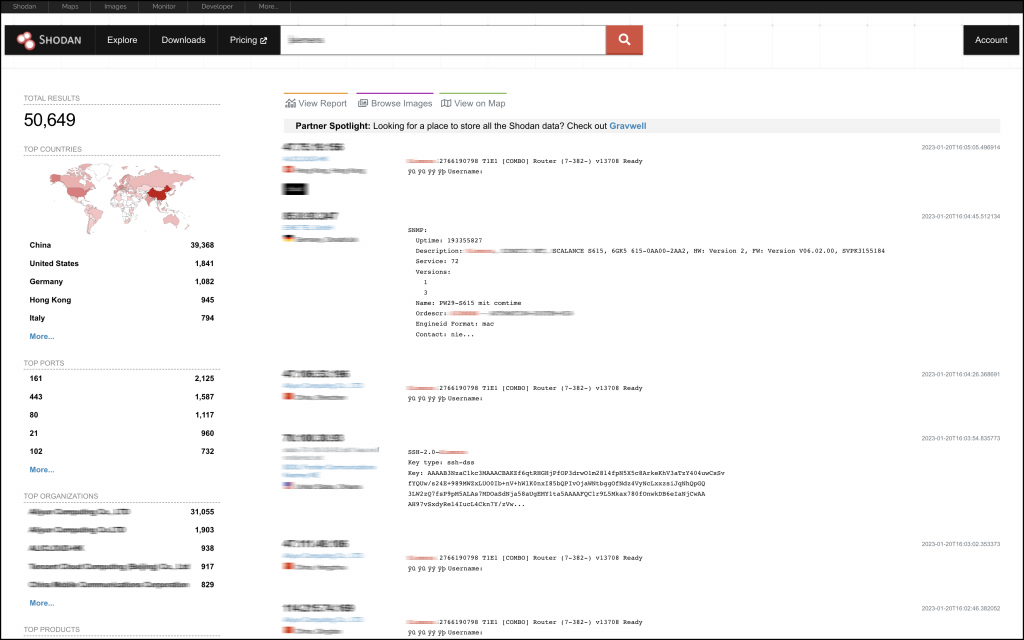
To quickly filter the results, you can select a data point from the left menu, such as country or product. If you want to dig deeper, you can run more intricate queries, configure notifications, and even integrate with the Shodan API.
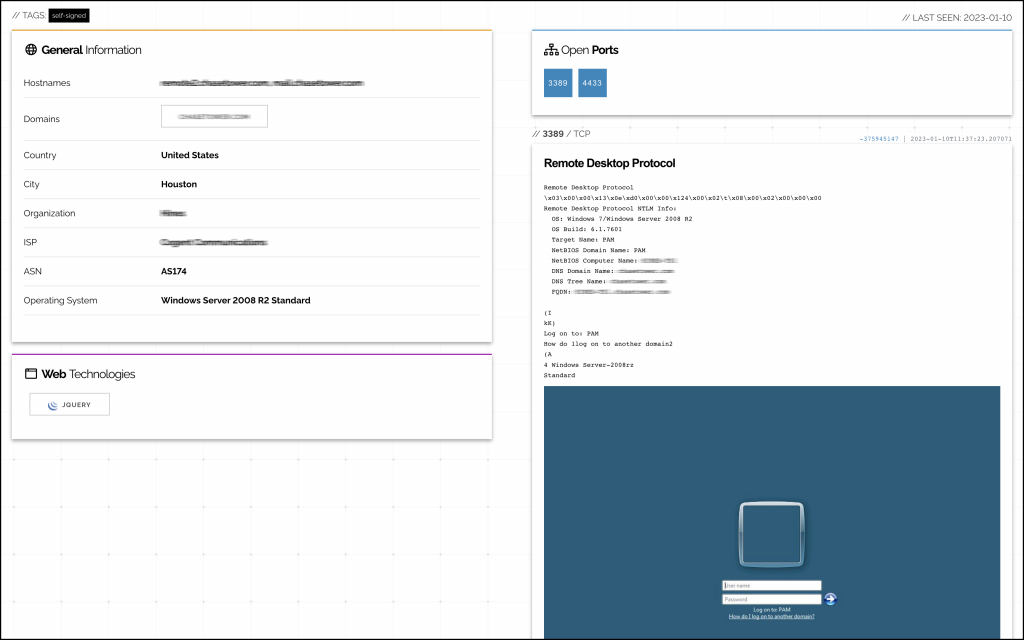
We selected one of the devices and can see some location details, hostname, company information, and even a Remote Desktop login screen.
What do you do if you find one of your devices in Shodan? Any connected device that is publicly exposed is a potential vulnerability and compromises a zero-trust architecture. To mitigate this risk, implement a proactive yet simple security solution such as View Secure Edge that centrally manages your building devices and networks. One of our clients identified seven properties with exposed devices (public IP addresses and remote desktop session feeds) and through the installation of Secure Edge was able to remove them from the public Shodan directory. Contact us for an initial consultation and risk assessment.

